Want to see Parasoft in action? Sign up for our Monthly Demos! See Demos & Events >>
Want to see Parasoft in action? Sign up for our Monthly Demos! See Demos & Events >>
 Reading Time: 7 minutes
Reading Time: 7 minutesLet's delve into answers to pressing OWASP Top 10 and web application security questions:
In software development, testing for software weaknesses that expose security vulnerabilities is routine. Web application security, however, has become more complex giving the growing use of application programming interfaces (APIs) that increase an attack surface for applications. DevSecOps, AppSec, and application development teams are now seeking practices to mitigate the security risks, reduce the attack surface and prevent data exposures caused by web application vulnerabilities.
There’s been an onslaught of web application attacks on organizations and it’s steadily increasing. Web applications are known to use vulnerable third-party dependencies. The accessibility and reachability of these vulnerable components have software dependencies that create security risks and expose attack surfaces in web applications. It makes it easy for attackers to create serious disruptions, steal, or tamper with personal information such as credit card data, cause a denial of service, or simply hold the data for ransom. Unfortunately, no business, big or small, gets a pass when it comes to these cybersecurity challenges.
Attackers seek out vulnerabilities and use them to compromise the application’s security. Web application vulnerabilities can be software weaknesses in the application code or misconfiguration issues in web based applications. These vulnerabilities can be the result of:
Web application attacks are one the most prevalent attack vectors for cybersecurity incidents and data breaches, as indicated in Verizon's 2021 Data Breach Investigation Report (DBIR). They require sound preventive and remediation strategies like patching and threat modeling to mitigate.
The Open Web Application Security Project (OWASP) is advancing application security (AppSec) practices globally through community engagement, training, and awareness. OWASP Top 10 is the reference standard for organizations that are proactively protecting web applications from security threats to reduce risks. OWASP Top 10 compliance validation is a good first step when attempting to change and improve the software development culture in your organization because of the education and awareness OWASP provides about application threats and things that can go wrong if good coding and application security practices are not followed.
Another resource for improving web application security is the Common Vulnerabilities and Exposures (CVE) system provides a reference to known information-security vulnerabilities and exposures. It allows everyone to keep track of publicly known vulnerabilities and provides telemetry on real world exploits that can be codified in software development practices and threat modeling activities to build security-in.
Web application scanning or testing (such as SAST, DAST, IAST, SCA) is a good foundation for security teams. A web application firewall (WAF) is yet another tool for filtering, monitoring, and blocking web application attacks identified in the OWASP Top 10.
The OWASP Top 10 is a list of the most known vulnerabilities and dangerous security risks for web applications. It's updated periodically to stay ahead of increasing and evolving threats.
OWASP provides documentation for the Top 10 list, with a website dedicated to each vulnerability, that outlines the threat, risk, and mitigation strategies. The site describes what each vulnerability is and provides a risk score, which is used to help prioritize and triage possible vulnerabilities.
The following vulnerabilities A1-A10 comprise the new OWASP Top 10 for 2021.
Topping the list as the most serious web application security risk, broken access control had 34 CWEs mapped to it. That’s more than occurrences in applications than any other category. A web application’s access control model is closely tied to the content and functions that the site provides. If it’s not configured properly, hackers can gain access to sensitive files and deface the site.
Cryptanalytic software involves different software programs used to crack encryptions. Formally called Sensitive Data Exposure, a cryptographic failure means the information that is supposed to be protected from untrusted sources has been disclosed to attackers. Hackers can then access information such as credit card processor data or any other authentication credentials.
When an attacker uses malicious SQL code to manipulate a backend database so it reveals sensitive information it’s called an injection attack. Injection flaws, such as NoSQL, OS, LDAP, and SQL injection, occur when untrusted data is sent to an interpreter as part of a command or query.
Cross-Site Scripting (XSS) attacks are another type of injection. Malicious scripts are injected into otherwise benign and trusted websites that can rewrite the content of the HTML page.
Sever-Side Request Forgery (SSRF) is a type of attack that can occur when a hacker can not only view unauthorized lists, delete tables and have unauthorized administrative access but also perform remote code execution from the back-end server of a vulnerable web application.
This is a new category for 2021 and the focus is on the risks related to design flaws. More threat modeling, secure design patterns and principles, and reference architectures are needed to protect against insecure designs for web pages.
This is an important addition because developers need to be aware of how design and architectural concepts need to be configured and implemented correctly in code. Implementing design and architectural concepts incorrectly in code can create security vulnerabilities.
XML External Entities attacks have been rolled into security misconfiguration this year. It’s an increasing threat because of more shifts in software configurations.
Previously titled Using Components with Known Vulnerabilities, this category represents a known issue that OWASP experts have found that many continue to struggle to test for risk assessment.
Many security issues have been attributed to outdated third-party software components. This is further compounded by a growing concern that the time to exploit is shrinking and organizations are not patching or remediating vulnerabilities fast enough.
Authentication vulnerabilities as a category have dropped from the second position in the top ten because the increased availability of standardized frameworks seems to be helping. It was previously called Broken Authentication vulnerability because it can result in a denial of service when user accounts aren’t able to be authenticated. Multi-factor authentication isn’t deployed in most instances. It now includes CWEs that are more related to identification failures.
As a new category for 2021, this focuses on making assumptions related to software updates, critical data, and CI/CD pipelines without verifying integrity. A8:2017—Insecure Deserialization is now a part of this larger category.
The growing concerns over recent attacks associated with the SolarWinds breach and securing the build environment increases the importance of this threat. Software integrity has been called out specifically in the Executive Order on Cybersecurity, section 4.
This category has been expanded to include more types of failures that can directly impact visibility, incident alerting, and forensics.
The data show there is a low incidence rate for this category that has just been added to the Top 10.
Because cyberattacks are constantly in the news, you cannot afford for your web applications to fall prey to attackers because of security vulnerabilities that can be avoided. Static application security testing (SAST), also known as static code analysis, allows your organization to perform automated testing and analysis of your web application source code.
SAST is the process of parsing through the code to check for software weaknesses that could expose security vulnerabilities in web applications. SAST tools don’t need a running application to perform an analysis. SAST can analyze code in real time to let you know about OWASP Top 10 violations sooner rather than later.
A good practice for reducing security vulnerabilities is to embed the guidance from the OWASP Top 10 into your software development activities from the start and use static application security testing to validate compliance. By incorporating static application security testing early in the development process, you can identify security weaknesses and any application vulnerability—when they are the easiest and least expensive to fix while meeting your security compliance mandates.
Dealing with the output of security tools can be overwhelming so you’ll want to look for automated SAST tools that incorporate a few security industry risk models. OWASP is a good place to start because it addresses the most important issues and vulnerabilities. You can improve upon that once your team feels they’ve got it under control. The expanded secure coding standards listed in the table below will help you broaden your security and set you up for future success.
| Coding Standard Name | Maintained By | Purpose Summary |
|---|---|---|
| CERT (Computer Emergency Response Team) | CERT Coordination Center | Guidelines to help developers avoid errors during coding and implementation, and also detect low level errors in design. |
| OWASP Top Ten | OWASP (Open Web Application Security Project) Foundation | Web application and software developers use these standards to identify and remedy high- security risks in web applications. |
| CWE (Common Weakness Enumeration) | Community developed and maintained. | This is a category system that helps developers identify vulnerabilities and weaknesses in software, and assists them in understanding software flaws. Developers also use the system to develop tools to fix and prevent flaws. |
| DISA Application Security and Development STIGS | Defense Information Systems Agency (DISA), and division of the United States Department of Defense. | Helps managers, designers, developers, and system administrators in developing and maintaining security controls in applications and application development. |
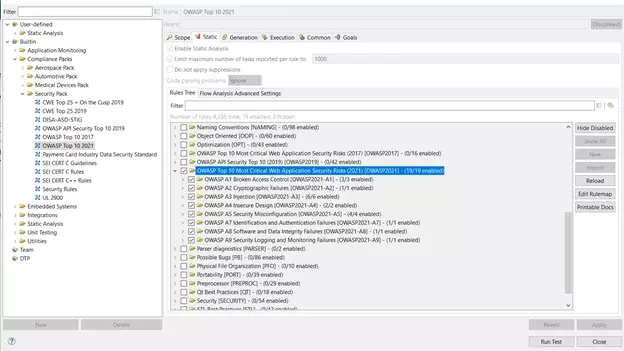
Automated SAST solutions like Parasoft offer an updated compliance pack per the OWASP updates. The new rules become checkers to help developers enforce the new secure coding practices, as shown in the image below, for popular programming languages like Java, C/C++, .NET, Python). This helps guide developers by eliminating the top ten risks that have been identified by OWASP. Additionally, a feature like automated prioritization leveraging AI/ML can take the guesswork out of manual triage.
The image below displays Parasoft's checkers/rules support for the updated version of the OWASP Top 10 2021.
Another weapon in your web application security toolbox is dynamic application security testing (DAST). With DAST, malicious attacks and other external behaviors are stimulated by searching for ways to exploit security vulnerabilities during runtime or black-box testing.
So, while SAST analyses every line of code without running the application, with DAST you’ll need to execute the application before it can start scanning for vulnerabilities, which is as soon as you have running software.
Deciding about static and dynamic code analysis for your organization depends on many variables. Read our blog post about SAST where there’s a great side-by-side comparison of the two tools.
Kevin, Director of Security Solutions at Parasoft, has extensive experience and expertise in software security, cyber research and development, and DevOps. He leverages his knowledge to create meaningful solutions and technologies to improve software security practices.